Bomb Lab
Introduction
Lab 2 for CSCI 2400 @ CU Boulder - Computer Systems
The nefarious Dr. Evil has planted a slew of “binary bombs” on our class machines. A binary bomb is a program that consists of a sequence of phases. Each phase expects you to type a particular string on stdin. If you type the correct string, then the phase is defused and the bomb proceeds to the next phase. Otherwise, the bomb explodes by printing "BOOM!!!" and then terminating. The bomb is defused when every phase has been defused.
There are too many bombs for us to deal with, so we are giving each student a bomb to defuse. Your mission, which you have no choice but to accept, is to defuse your bomb before the due date. Good luck, and welcome to the bomb squad! Bomb Lab Handout
I like using objdump to disassemble the code and get a broad overview of what is happening before I start.
objdump -d bomb > dis.txt
Note: I am not sure about the history of the bomb lab. I think it started at CMU.
Phase 1
joxxxn@jupyter-nxxh6xx8:~/lab2-bomblab-navanchauhan/bombbomb$ gdb -ex 'break phase_1' -ex 'break explode_bomb' -ex 'run' ./bomb
GNU gdb (Ubuntu 12.1-0ubuntu1~22.04) 12.1
Copyright (C) 2022 Free Software Foundation, Inc.
License GPLv3+: GNU GPL version 3 or later <http://gnu.org/licenses/gpl.html>
This is free software: you are free to change and redistribute it.
There is NO WARRANTY, to the extent permitted by law.
Type "show copying" and "show warranty" for details.
This GDB was configured as "x86_64-linux-gnu".
Type "show configuration" for configuration details.
For bug reporting instructions, please see:
<https://www.gnu.org/software/gdb/bugs/>.
Find the GDB manual and other documentation resources online at:
<http://www.gnu.org/software/gdb/documentation/>.
For help, type "help".
Type "apropos word" to search for commands related to "word"...
Reading symbols from ./bomb...
Breakpoint 1 at 0x15c7
Breakpoint 2 at 0x1d4a
Starting program: /home/joxxxn/lab2-bomblab-navanchauhan/bombbomb/bomb
[Thread debugging using libthread_db enabled]
Using host libthread_db library "/lib/x86_64-linux-gnu/libthread_db.so.1".
Welcome to my fiendish little bomb. You have 6 phases with
which to blow yourself up. Have a nice day!
test string
Breakpoint 1, 0x00005555555555c7 in phase_1 ()
(gdb) dias phase_1
Undefined command: "dias". Try "help".
(gdb) disas phase_1
Dump of assembler code for function phase_1:
=> 0x00005555555555c7 <+0>: endbr64
0x00005555555555cb <+4>: sub $0x8,%rsp
0x00005555555555cf <+8>: lea 0x1b7a(%rip),%rsi # 0x555555557150
0x00005555555555d6 <+15>: call 0x555555555b31 <strings_not_equal>
0x00005555555555db <+20>: test %eax,%eax
0x00005555555555dd <+22>: jne 0x5555555555e4 <phase_1+29>
0x00005555555555df <+24>: add $0x8,%rsp
0x00005555555555e3 <+28>: ret
0x00005555555555e4 <+29>: call 0x555555555d4a <explode_bomb>
0x00005555555555e9 <+34>: jmp 0x5555555555df <phase_1+24>
End of assembler dump.
(gdb) print 0x555555557150
$1 = 93824992244048
(gdb) x/1s 0x555555557150
0x555555557150: "Controlling complexity is the essence of computer programming."
(gdb)
Phase 2
Phase 1 defused. How about the next one?
1 2 3 4 5 6
Breakpoint 1, 0x00005555555555eb in phase_2 ()
(gdb) disas
Dump of assembler code for function phase_2:
=> 0x00005555555555eb <+0>: endbr64
0x00005555555555ef <+4>: push %rbp
0x00005555555555f0 <+5>: push %rbx
0x00005555555555f1 <+6>: sub $0x28,%rsp
0x00005555555555f5 <+10>: mov %rsp,%rsi
0x00005555555555f8 <+13>: call 0x555555555d97 <read_six_numbers>
0x00005555555555fd <+18>: cmpl $0x0,(%rsp)
0x0000555555555601 <+22>: js 0x55555555560d <phase_2+34>
0x0000555555555603 <+24>: mov %rsp,%rbp
0x0000555555555606 <+27>: mov $0x1,%ebx
0x000055555555560b <+32>: jmp 0x555555555620 <phase_2+53>
0x000055555555560d <+34>: call 0x555555555d4a <explode_bomb>
0x0000555555555612 <+39>: jmp 0x555555555603 <phase_2+24>
0x0000555555555614 <+41>: add $0x1,%ebx
0x0000555555555617 <+44>: add $0x4,%rbp
0x000055555555561b <+48>: cmp $0x6,%ebx
0x000055555555561e <+51>: je 0x555555555631 <phase_2+70>
0x0000555555555620 <+53>: mov %ebx,%eax
0x0000555555555622 <+55>: add 0x0(%rbp),%eax
0x0000555555555625 <+58>: cmp %eax,0x4(%rbp)
0x0000555555555628 <+61>: je 0x555555555614 <phase_2+41>
0x000055555555562a <+63>: call 0x555555555d4a <explode_bomb>
0x000055555555562f <+68>: jmp 0x555555555614 <phase_2+41>
0x0000555555555631 <+70>: add $0x28,%rsp
0x0000555555555635 <+74>: pop %rbx
0x0000555555555636 <+75>: pop %rbp
0x0000555555555637 <+76>: ret
End of assembler dump.
(gdb)
0x00005555555555fd <+18>: cmpl $0x0,(%rsp)
0x0000555555555601 <+22>: js 0x55555555560d <phase_2+34>
...
0x000055555555560d <+34>: call 0x555555555d4a <explode_bomb>
The program first compares if the first number is not 0. If the number is not 0, then the cmpl instruction returns a negative value. The js instruction stands for jump if sign -> causing a jump to the specified address if the sign bit is set. This would result in the explode_bomb function being called.
0x0000555555555603 <+24>: mov %rsp,%rbp
0x0000555555555606 <+27>: mov $0x1,%ebx
%rsp in x86-64 asm, is the stack pointer i.e. it points to the top of the current stack frame. Since the program just read six numbers, the top of the stack (%rsp) contains the address of the first number.
By executing mov %rsp,%rbp we are setting the base pointer (%rbp) to point to this address.
Now, for the second instruction mov $0x1,%ebx, we are initialising the %ebx register with the value 1. Based on the assembly code, you can see that this is being used as a counter/index for the loop.
0x000055555555560b <+32>: jmp 0x555555555620 <phase_2+53>
The program now jumps to
0x0000555555555620 <+53>: mov %ebx,%eax
0x0000555555555622 <+55>: add 0x0(%rbp),%eax
0x0000555555555625 <+58>: cmp %eax,0x4(%rbp)
0x0000555555555628 <+61>: je 0x555555555614 <phase_2+41>
Here, the value from %ebx is copied to the %eax register. For this iteration, the value should be 1.
Then, the value at the memory location pointed by %rbp is added to the value in %eax. For now, 0 is added (the first number that we read).
cmp %eax,0x4(%rbp) - The instruction compares the value in %eax to the value at the memory address %rbp + 4. Since Integers in this context are stored using a word of memory of 4 bytes, this indicates it checks against the second number in the sequence.
je 0x555555555614 <phase_2+41> - The program will jump to phase_2+41 if the previous cmp instruction determined the values as equal.
0x0000555555555614 <+41>: add $0x1,%ebx
0x0000555555555617 <+44>: add $0x4,%rbp
0x000055555555561b <+48>: cmp $0x6,%ebx
0x000055555555561e <+51>: je 0x555555555631 <phase_2+70>
0x0000555555555620 <+53>: mov %ebx,%eax
0x0000555555555622 <+55>: add 0x0(%rbp),%eax
0x0000555555555625 <+58>: cmp %eax,0x4(%rbp)
0x0000555555555628 <+61>: je 0x555555555614 <phase_2+41>
Here, we can see that the program increments %ebx by 1, adds a 4 byte offset to %rbp (the number we will be matching now), and checks if %ebx is equal to 6. If it is, it breaks the loop and jumps to <phase_2+70> successfully finishing this stage.
Now, given that we know the first two numbers in the sequence are 0 1, we can calculate the other numbers by following the pattern of adding the counter and the value of the previous number.
Thus,
- 3rd number = 1 (previous value) + 2 = 3
- 4th number = 3 (prev value) + 3 = 6
- 5th number = 6 (prev value) + 4 = 10
- 6th number = 10 (prev value) + 5 = 15
...
Phase 1 defused. How about the next one?
0 1 3 6 10 15
Breakpoint 1, 0x00005555555555eb in phase_2 ()
(gdb) continue
Continuing.
That's number 2. Keep going!
Phase 3
Let us look at the disassembled code first
0000000000001638 <phase_3>:
1638: f3 0f 1e fa endbr64
163c: 48 83 ec 18 sub $0x18,%rsp
1640: 48 8d 4c 24 07 lea 0x7(%rsp),%rcx
1645: 48 8d 54 24 0c lea 0xc(%rsp),%rdx
164a: 4c 8d 44 24 08 lea 0x8(%rsp),%r8
164f: 48 8d 35 60 1b 00 00 lea 0x1b60(%rip),%rsi # 31b6 <_IO_stdin_used+0x1b6>
1656: b8 00 00 00 00 mov $0x0,%eax
165b: e8 80 fc ff ff call 12e0 <__isoc99_sscanf@plt>
1660: 83 f8 02 cmp $0x2,%eax
1663: 7e 20 jle 1685 <phase_3+0x4d>
1665: 83 7c 24 0c 07 cmpl $0x7,0xc(%rsp)
166a: 0f 87 0d 01 00 00 ja 177d <phase_3+0x145>
1670: 8b 44 24 0c mov 0xc(%rsp),%eax
1674: 48 8d 15 55 1b 00 00 lea 0x1b55(%rip),%rdx # 31d0 <_IO_stdin_used+0x1d0>
167b: 48 63 04 82 movslq (%rdx,%rax,4),%rax
167f: 48 01 d0 add %rdx,%rax
1682: 3e ff e0 notrack jmp *%rax
1685: e8 c0 06 00 00 call 1d4a <explode_bomb>
168a: eb d9 jmp 1665 <phase_3+0x2d>
168c: b8 63 00 00 00 mov $0x63,%eax
1691: 81 7c 24 08 3d 02 00 cmpl $0x23d,0x8(%rsp)
1698: 00
1699: 0f 84 e8 00 00 00 je 1787 <phase_3+0x14f>
169f: e8 a6 06 00 00 call 1d4a <explode_bomb>
16a4: b8 63 00 00 00 mov $0x63,%eax
16a9: e9 d9 00 00 00 jmp 1787 <phase_3+0x14f>
16ae: b8 61 00 00 00 mov $0x61,%eax
16b3: 81 7c 24 08 27 01 00 cmpl $0x127,0x8(%rsp)
16ba: 00
16bb: 0f 84 c6 00 00 00 je 1787 <phase_3+0x14f>
16c1: e8 84 06 00 00 call 1d4a <explode_bomb>
16c6: b8 61 00 00 00 mov $0x61,%eax
16cb: e9 b7 00 00 00 jmp 1787 <phase_3+0x14f>
16d0: b8 78 00 00 00 mov $0x78,%eax
16d5: 81 7c 24 08 e7 02 00 cmpl $0x2e7,0x8(%rsp)
16dc: 00
16dd: 0f 84 a4 00 00 00 je 1787 <phase_3+0x14f>
16e3: e8 62 06 00 00 call 1d4a <explode_bomb>
16e8: b8 78 00 00 00 mov $0x78,%eax
16ed: e9 95 00 00 00 jmp 1787 <phase_3+0x14f>
16f2: b8 64 00 00 00 mov $0x64,%eax
16f7: 81 7c 24 08 80 02 00 cmpl $0x280,0x8(%rsp)
16fe: 00
16ff: 0f 84 82 00 00 00 je 1787 <phase_3+0x14f>
1705: e8 40 06 00 00 call 1d4a <explode_bomb>
170a: b8 64 00 00 00 mov $0x64,%eax
170f: eb 76 jmp 1787 <phase_3+0x14f>
1711: b8 6d 00 00 00 mov $0x6d,%eax
1716: 81 7c 24 08 ff 02 00 cmpl $0x2ff,0x8(%rsp)
171d: 00
171e: 74 67 je 1787 <phase_3+0x14f>
1720: e8 25 06 00 00 call 1d4a <explode_bomb>
1725: b8 6d 00 00 00 mov $0x6d,%eax
172a: eb 5b jmp 1787 <phase_3+0x14f>
172c: b8 71 00 00 00 mov $0x71,%eax
1731: 81 7c 24 08 75 03 00 cmpl $0x375,0x8(%rsp)
1738: 00
1739: 74 4c je 1787 <phase_3+0x14f>
173b: e8 0a 06 00 00 call 1d4a <explode_bomb>
1740: b8 71 00 00 00 mov $0x71,%eax
1745: eb 40 jmp 1787 <phase_3+0x14f>
1747: b8 79 00 00 00 mov $0x79,%eax
174c: 81 7c 24 08 94 02 00 cmpl $0x294,0x8(%rsp)
1753: 00
1754: 74 31 je 1787 <phase_3+0x14f>
1756: e8 ef 05 00 00 call 1d4a <explode_bomb>
175b: b8 79 00 00 00 mov $0x79,%eax
1760: eb 25 jmp 1787 <phase_3+0x14f>
1762: b8 79 00 00 00 mov $0x79,%eax
1767: 81 7c 24 08 88 02 00 cmpl $0x288,0x8(%rsp)
176e: 00
176f: 74 16 je 1787 <phase_3+0x14f>
1771: e8 d4 05 00 00 call 1d4a <explode_bomb>
1776: b8 79 00 00 00 mov $0x79,%eax
177b: eb 0a jmp 1787 <phase_3+0x14f>
177d: e8 c8 05 00 00 call 1d4a <explode_bomb>
1782: b8 68 00 00 00 mov $0x68,%eax
1787: 38 44 24 07 cmp %al,0x7(%rsp)
178b: 75 05 jne 1792 <phase_3+0x15a>
178d: 48 83 c4 18 add $0x18,%rsp
1791: c3 ret
1792: e8 b3 05 00 00 call 1d4a <explode_bomb>
1797: eb f4 jmp 178d <phase_3+0x155>
...
165b: e8 80 fc ff ff call 12e0 <__isoc99_sscanf@plt>
...
We can see that scanf is being called which means we need to figure out what datatype(s) the program is expecting.
Because I do not want to enter the solutions to phases 1 and 2 again and again, I am goig to pass a file which has these solutions.
joxxxn@jupyter-nxxh6xx8:~/lab2-bomblab-navanchauhan/bombbomb$ gdb -ex 'break phase_3' -ex 'break explode_bomb' -ex 'run' -args ./bomb sol.txt
GNU gdb (Ubuntu 12.1-0ubuntu1~22.04) 12.1
Copyright (C) 2022 Free Software Foundation, Inc.
License GPLv3+: GNU GPL version 3 or later <http://gnu.org/licenses/gpl.html>
This is free software: you are free to change and redistribute it.
There is NO WARRANTY, to the extent permitted by law.
Type "show copying" and "show warranty" for details.
This GDB was configured as "x86_64-linux-gnu".
Type "show configuration" for configuration details.
For bug reporting instructions, please see:
<https://www.gnu.org/software/gdb/bugs/>.
Find the GDB manual and other documentation resources online at:
<http://www.gnu.org/software/gdb/documentation/>.
For help, type "help".
Type "apropos word" to search for commands related to "word"...
Reading symbols from ./bomb...
Breakpoint 1 at 0x1638
Breakpoint 2 at 0x1d4a
Starting program: /home/joxxxn/lab2-bomblab-navanchauhan/bombbomb/bomb sol.txt
[Thread debugging using libthread_db enabled]
Using host libthread_db library "/lib/x86_64-linux-gnu/libthread_db.so.1".
Welcome to my fiendish little bomb. You have 6 phases with
which to blow yourself up. Have a nice day!
Phase 1 defused. How about the next one?
That's number 2. Keep going!
random string
Breakpoint 1, 0x0000555555555638 in phase_3 ()
(gdb) disas
Dump of assembler code for function phase_3:
=> 0x0000555555555638 <+0>: endbr64
0x000055555555563c <+4>: sub $0x18,%rsp
0x0000555555555640 <+8>: lea 0x7(%rsp),%rcx
0x0000555555555645 <+13>: lea 0xc(%rsp),%rdx
0x000055555555564a <+18>: lea 0x8(%rsp),%r8
0x000055555555564f <+23>: lea 0x1b60(%rip),%rsi # 0x5555555571b6
0x0000555555555656 <+30>: mov $0x0,%eax
0x000055555555565b <+35>: call 0x5555555552e0 <__isoc99_sscanf@plt>
0x0000555555555660 <+40>: cmp $0x2,%eax
0x0000555555555663 <+43>: jle 0x555555555685 <phase_3+77>
0x0000555555555665 <+45>: cmpl $0x7,0xc(%rsp)
0x000055555555566a <+50>: ja 0x55555555577d <phase_3+325>
0x0000555555555670 <+56>: mov 0xc(%rsp),%eax
0x0000555555555674 <+60>: lea 0x1b55(%rip),%rdx # 0x5555555571d0
0x000055555555567b <+67>: movslq (%rdx,%rax,4),%rax
0x000055555555567f <+71>: add %rdx,%rax
0x0000555555555682 <+74>: notrack jmp *%rax
0x0000555555555685 <+77>: call 0x555555555d4a <explode_bomb>
0x000055555555568a <+82>: jmp 0x555555555665 <phase_3+45>
0x000055555555568c <+84>: mov $0x63,%eax
0x0000555555555691 <+89>: cmpl $0x23d,0x8(%rsp)
0x0000555555555699 <+97>: je 0x555555555787 <phase_3+335>
0x000055555555569f <+103>: call 0x555555555d4a <explode_bomb>
0x00005555555556a4 <+108>: mov $0x63,%eax
0x00005555555556a9 <+113>: jmp 0x555555555787 <phase_3+335>
--Type <RET> for more, q to quit, c to continue without paging--
gdb has thankfully marked the address which is being passed to scanf. We can access the value:
(gdb) x/1s 0x5555555571b6
0x5555555571b6: "%d %c %d"
(gdb)
BINGO! The program expects an integer, character, and another integer. Onwards.
0x0000555555555660 <+40>: cmp $0x2,%eax
0x0000555555555663 <+43>: jle 0x555555555685 <phase_3+77>
...
0x0000555555555685 <+77>: call 0x555555555d4a <explode_bomb>
The program checks whether scanf returns a value <= 2, if it does then it calls the explode_bomb function.
Note: scanf returns the number of fields that were successfully converted and assigned
0x0000555555555665 <+45>: cmpl $0x7,0xc(%rsp)
0x000055555555566a <+50>: ja 0x55555555577d <phase_3+325>
...
0x000055555555577d <+325>: call 0x555555555d4a <explode_bomb>
Similarly, the program checks and ensures the returned value is not > 7.
0x0000555555555670 <+56>: mov 0xc(%rsp),%eax
0x0000555555555674 <+60>: lea 0x1b55(%rip),%rdx # 0x5555555571d0
0x000055555555567b <+67>: movslq (%rdx,%rax,4),%rax
0x000055555555567f <+71>: add %rdx,%rax
0x0000555555555682 <+74>: notrack jmp *%rax
0x0000555555555685 <+77>: call 0x555555555d4a <explode_bomb>
0x0000555555555670 <+56>: mov 0xc(%rsp),%eax- Moves value located at0xc(12 in Decimal) bytes above the stack pointer to%eaxregister.0x0000555555555674 <+60>: lea 0x1b55(%rip),%rdx # 0x5555555571d0- This instruction calculates an effective address by adding0x1b55to the current instruction pointer (%rip). The result is stored in the%rdxregister.0x000055555555567b <+67>: movslq (%rdx,%rax,4),%raxmovslqstands for "move with sign-extension from a 32-bit value to a 64-bit value." (if the 32-bit value is negative, the 64-bit result will have all its upper 32 bits set to 1; otherwise, they'll be set to 0).(%rdx,%rax,4)- First start with the value in the %rdx register, then add to it the value in the %rax register multiplied by 4.%rax- Destination Register
0x000055555555567f <+71>: add %rdx,%rax- Adds base address in%rdxto the offset in%rax0x0000555555555682 <+74>: notrack jmp *%rax- Jumps to the address stored in%rax0x0000555555555685 <+77>: call 0x555555555d4a <explode_bomb>- If we are unable to jump to the specified instruction, callexplode_bomb
Let us try to run the program again with a valid input for the first number and see what the program is computing for the address.
I used the input: 3 c 123.
To check what is the computed address, we can switch to the asm layout by running layout asm, and then going through instructions ni or si until we reach the line movslq (%rdx,%rax,4),%rax
%rax should hold the value 3.
(gdb) print $rax
$1 = 3
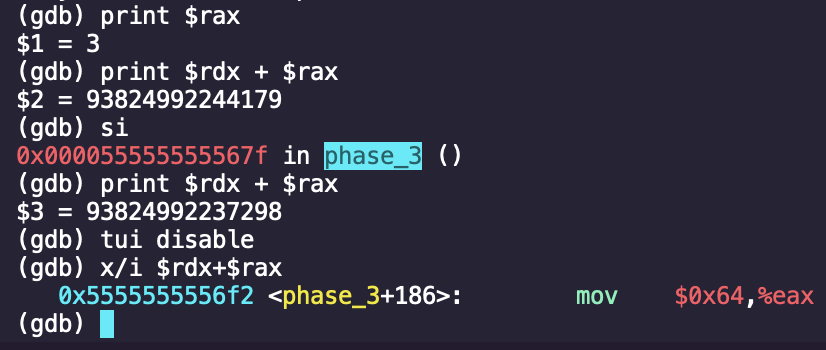
We can see that this makes us jump to <phase_3+186> (Continue to step through the code by using ni)
0x00005555555556f2 <+186>: mov $0x64,%eax
0x00005555555556f7 <+191>: cmpl $0x280,0x8(%rsp)
0x00005555555556ff <+199>: je 0x555555555787 <phase_3+335>
0x0000555555555705 <+205>: call 0x555555555d4a <explode_bomb>
We see that 0x64 (Decimal 100) is being stored in %eax. Then, the program compares 0x280 (Decimal 640) with memory address 0x8 bytes above the stack pointer (%rsp). If the values are equal, then it jumps to <phase_3+335>, otherwise explode_bomb is called.
0x0000555555555787 <+335>: cmp %al,0x7(%rsp)
0x000055555555578b <+339>: jne 0x555555555792 <phase_3+346>
0x000055555555578d <+341>: add $0x18,%rsp
0x0000555555555791 <+345>: ret
0x0000555555555792 <+346>: call 0x555555555d4a <explode_bomb>
Here, the program is comparing the value of our given character to the value stored in %al (lower 8 bits of EAX), and checks if they are not equal.
Knowing that the character is stored at an offset of 7 bytes to %rsp, we can print and check the value by running:
(gdb) x/1cw $rsp+7
c
(gdb) print $al
$1 = 100
We can simply lookup the ASCII table, and see that 100 in decimal stands for the character d. Let us try this answer:
...
That's number 2. Keep going!
3 d 640
Breakpoint 1, 0x0000555555555638 in phase_3 ()
(gdb) continue
Continuing.
Halfway there!
Phase 4
joxxxn@jupyter-nxxh6xx8:~/lab2-bomblab-navanchauhan/bombbomb$ gdb -ex 'break phase_4' -ex 'break explode_bomb' -ex 'run' -args ./bomb sol.txt
GNU gdb (Ubuntu 12.1-0ubuntu1~22.04) 12.1
Copyright (C) 2022 Free Software Foundation, Inc.
License GPLv3+: GNU GPL version 3 or later <http://gnu.org/licenses/gpl.html>
This is free software: you are free to change and redistribute it.
There is NO WARRANTY, to the extent permitted by law.
Type "show copying" and "show warranty" for details.
This GDB was configured as "x86_64-linux-gnu".
Type "show configuration" for configuration details.
For bug reporting instructions, please see:
<https://www.gnu.org/software/gdb/bugs/>.
Find the GDB manual and other documentation resources online at:
<http://www.gnu.org/software/gdb/documentation/>.
For help, type "help".
Type "apropos word" to search for commands related to "word"...
Reading symbols from ./bomb...
Breakpoint 1 at 0x17d3
Breakpoint 2 at 0x1d4a
Starting program: /home/joxxxn/lab2-bomblab-navanchauhan/bombbomb/bomb sol.txt
[Thread debugging using libthread_db enabled]
Using host libthread_db library "/lib/x86_64-linux-gnu/libthread_db.so.1".
Welcome to my fiendish little bomb. You have 6 phases with
which to blow yourself up. Have a nice day!
Phase 1 defused. How about the next one?
That's number 2. Keep going!
Halfway there!
test string
Breakpoint 1, 0x00005555555557d3 in phase_4 ()
(gdb) disas phase_4
Dump of assembler code for function phase_4:
=> 0x00005555555557d3 <+0>: endbr64
0x00005555555557d7 <+4>: sub $0x18,%rsp
0x00005555555557db <+8>: lea 0x8(%rsp),%rcx
0x00005555555557e0 <+13>: lea 0xc(%rsp),%rdx
0x00005555555557e5 <+18>: lea 0x1bba(%rip),%rsi # 0x5555555573a6
0x00005555555557ec <+25>: mov $0x0,%eax
0x00005555555557f1 <+30>: call 0x5555555552e0 <__isoc99_sscanf@plt>
0x00005555555557f6 <+35>: cmp $0x2,%eax
0x00005555555557f9 <+38>: jne 0x555555555802 <phase_4+47>
0x00005555555557fb <+40>: cmpl $0xe,0xc(%rsp)
0x0000555555555800 <+45>: jbe 0x555555555807 <phase_4+52>
0x0000555555555802 <+47>: call 0x555555555d4a <explode_bomb>
0x0000555555555807 <+52>: mov $0xe,%edx
0x000055555555580c <+57>: mov $0x0,%esi
0x0000555555555811 <+62>: mov 0xc(%rsp),%edi
0x0000555555555815 <+66>: call 0x555555555799 <func4>
0x000055555555581a <+71>: cmp $0x2,%eax
0x000055555555581d <+74>: jne 0x555555555826 <phase_4+83>
0x000055555555581f <+76>: cmpl $0x2,0x8(%rsp)
0x0000555555555824 <+81>: je 0x55555555582b <phase_4+88>
0x0000555555555826 <+83>: call 0x555555555d4a <explode_bomb>
0x000055555555582b <+88>: add $0x18,%rsp
0x000055555555582f <+92>: ret
End of assembler dump.
(gdb)
Again, gdb has marked the string being passed to scanf
(gdb) x/1s 0x5555555573a6
0x5555555573a6: "%d %d"
Okay, so this time we are supposed to enter 2 numbers.
0x00005555555557f6 <+35>: cmp $0x2,%eax
0x00005555555557f9 <+38>: jne 0x555555555802 <phase_4+47>
Checks if there were 2 values read from calling scanf, if not -> jump to <phase_4+47> which calls <explode_bomb>.
0x00005555555557fb <+40>: cmpl $0xe,0xc(%rsp)
0x0000555555555800 <+45>: jbe 0x555555555807 <phase_4+52>
Compare 0xe (14 in Decimal) and value stored at $rsp + 0xc bytes (Decimal 12). If this condition is met (<= 14), jump to <phase_4+52>. If not, then explode bomb.
...
0x0000555555555807 <+52>: mov $0xe,%edx
0x000055555555580c <+57>: mov $0x0,%esi
0x0000555555555811 <+62>: mov 0xc(%rsp),%edi
0x0000555555555815 <+66>: call 0x555555555799 <func4>
0x000055555555581a <+71>: cmp $0x2,%eax
0x000055555555581d <+74>: jne 0x555555555826 <phase_4+83>
0x000055555555581f <+76>: cmpl $0x2,0x8(%rsp)
0x0000555555555824 <+81>: je 0x55555555582b <phase_4+88>
0x0000555555555826 <+83>: call 0x555555555d4a <explode_bomb>
0x0000555555555815 <+66>: call 0x555555555799 <func4>calls another function calledfunc4- The returned value is compared with
0x2, if they are not equal then the program jumps to call<explode_bomb>. This tells us thatfunc4should return 2.
Let us look into func4
(gdb) disas func4
Dump of assembler code for function func4:
0x0000555555555799 <+0>: endbr64
0x000055555555579d <+4>: sub $0x8,%rsp
0x00005555555557a1 <+8>: mov %edx,%ecx
0x00005555555557a3 <+10>: sub %esi,%ecx
0x00005555555557a5 <+12>: shr %ecx
0x00005555555557a7 <+14>: add %esi,%ecx
0x00005555555557a9 <+16>: cmp %edi,%ecx
0x00005555555557ab <+18>: ja 0x5555555557b9 <func4+32>
0x00005555555557ad <+20>: mov $0x0,%eax
0x00005555555557b2 <+25>: jb 0x5555555557c5 <func4+44>
0x00005555555557b4 <+27>: add $0x8,%rsp
0x00005555555557b8 <+31>: ret
0x00005555555557b9 <+32>: lea -0x1(%rcx),%edx
0x00005555555557bc <+35>: call 0x555555555799 <func4>
0x00005555555557c1 <+40>: add %eax,%eax
0x00005555555557c3 <+42>: jmp 0x5555555557b4 <func4+27>
0x00005555555557c5 <+44>: lea 0x1(%rcx),%esi
0x00005555555557c8 <+47>: call 0x555555555799 <func4>
0x00005555555557cd <+52>: lea 0x1(%rax,%rax,1),%eax
0x00005555555557d1 <+56>: jmp 0x5555555557b4 <func4+27>
This looks like a recursive function :( (I hate recursive functions)
Let's annotate the instructions.
endbr64
sub $0x8,%rsp // subtract 8 bytes from the stack pointer
mov %edx,%ecx // Move the value in register %edx to %ecx
sub %esi,%ecx // Subtract the value in %esi from %ecx
shr %ecx // Right shift the value in %ecx by one bit (dividing the value by 2)
add %esi,%ecx // Add the value in %esi to %ecx
cmp %edi,%ecx // Compare
ja 0x5555555557b9 <func4+32> // If %ecx > %edi -> jump to instruction at offset +32
mov $0x0,%eax // Move 0 to %eax
jb 0x5555555557c5 <func4+44> // If %ecx < %edi -> jump to instruction at offset +44.
add $0x8,%rsp // add 8 bytes to the stack pointer
ret // return
lea -0x1(%rcx),%edx // LEA of $rxc - 1 into $edx
call 0x555555555799 <func4> // Call itself
add %eax,%eax // Double the value in %eax
jmp 0x5555555557b4 <func4+27> // jump to the instruction at offset +27
lea 0x1(%rcx),%esi
call 0x555555555799 <func4>
lea 0x1(%rax,%rax,1),%eax // LEA of %rax * 2 + 1 into $eax
jmp 0x5555555557b4 <func4+27>
We can either try to compute the values by hand, or write a simple script in Python to get the answer.
def func4(edi, esi=0, edx=20):
ecx = (edx - esi) // 2 + esi
if ecx > edi:
return 2 * func4(edi, esi, ecx - 1)
elif ecx < edi:
return 2 * func4(edi, ecx + 1, edx) + 1
else:
return 0
for x in range(15): # We can limit to 14
if func4(x) == 2:
print(f"answer is {x}")
break
Running this code, we get: answer is 5
Okay, so we know that the number needed to be passed to func4 is 5. But, what about the second digit?
If we go back to the code for <phase_4>, we can see that:
0x000055555555581f <+76>: cmpl $0x2,0x8(%rsp)
0x0000555555555824 <+81>: je 0x55555555582b <phase_4+88>
The value at $rsp+8 should be equal to 2. So, let us try passing 5 2 as our input.
...
Phase 1 defused. How about the next one?
That's number 2. Keep going!
Halfway there!
5 2
Breakpoint 1, 0x00005555555557d3 in phase_4 ()
(gdb) continue
Continuing.
So you got that one. Try this one.
Phase 5
So you got that one. Try this one.
test string
Breakpoint 1, 0x0000555555555830 in phase_5 ()
(gdb) disas phase_5
Dump of assembler code for function phase_5:
=> 0x0000555555555830 <+0>: endbr64
0x0000555555555834 <+4>: push %rbx
0x0000555555555835 <+5>: sub $0x10,%rsp
0x0000555555555839 <+9>: mov %rdi,%rbx
0x000055555555583c <+12>: call 0x555555555b10 <string_length>
0x0000555555555841 <+17>: cmp $0x6,%eax
0x0000555555555844 <+20>: jne 0x55555555588b <phase_5+91>
0x0000555555555846 <+22>: mov $0x0,%eax
0x000055555555584b <+27>: lea 0x199e(%rip),%rcx # 0x5555555571f0 <array.0>
0x0000555555555852 <+34>: movzbl (%rbx,%rax,1),%edx
0x0000555555555856 <+38>: and $0xf,%edx
0x0000555555555859 <+41>: movzbl (%rcx,%rdx,1),%edx
0x000055555555585d <+45>: mov %dl,0x9(%rsp,%rax,1)
0x0000555555555861 <+49>: add $0x1,%rax
0x0000555555555865 <+53>: cmp $0x6,%rax
0x0000555555555869 <+57>: jne 0x555555555852 <phase_5+34>
0x000055555555586b <+59>: movb $0x0,0xf(%rsp)
0x0000555555555870 <+64>: lea 0x9(%rsp),%rdi
0x0000555555555875 <+69>: lea 0x1943(%rip),%rsi # 0x5555555571bf
0x000055555555587c <+76>: call 0x555555555b31 <strings_not_equal>
0x0000555555555881 <+81>: test %eax,%eax
0x0000555555555883 <+83>: jne 0x555555555892 <phase_5+98>
0x0000555555555885 <+85>: add $0x10,%rsp
0x0000555555555889 <+89>: pop %rbx
0x000055555555588a <+90>: ret
0x000055555555588b <+91>: call 0x555555555d4a <explode_bomb>
0x0000555555555890 <+96>: jmp 0x555555555846 <phase_5+22>
0x0000555555555892 <+98>: call 0x555555555d4a <explode_bomb>
0x0000555555555897 <+103>: jmp 0x555555555885 <phase_5+85>
End of assembler dump.
(gdb)
...
0x000055555555583c <+12>: call 0x555555555b10 <string_length>
0x0000555555555841 <+17>: cmp $0x6,%eax
0x0000555555555844 <+20>: jne 0x55555555588b <phase_5+91>
...
0x000055555555588b <+91>: call 0x555555555d4a <explode_bomb>
...
First things first, these instructions check to make sure the passed string is of length 6, otherwise explode_bomb is called.
We can also see a similar pattern compared to Phase 2, where we had a loop:
- The looping part:
mov $0x0,%eax- Initialise%eaxand set it to 0 (our counter/iterator)movzbl (%rbx,%rax,1),%edx- Access%rbx + 1 * %raxand store it in%edxand $0xf,%edx- Take the least significant 4 bits of the byte.movzbl (%rcx,%rdx,1),%edx- Use the 4 bits as an index into another array and load the corresponding byte into%edxmov %dl,0x9(%rsp,%rax,1)- Store the transformed byte into a buffer on the stackadd $0x1,%rax- Increment%raxcmp $0x6,%rax- If the index is not yet 6, loop again
movb $0x0,0xf(%rsp)- Null-terminate the transformed stringlea 0x9(%rsp),%rdiandlea 0x1943(%rip),%rsiall 0x555555555b31 <strings_not_equal>check if the two strings loaded up just before this are equal or not.
We can check the reference string we need, which gdb has marked as # 0x5555555571bf, and the lookup table marked as # 0x5555555571f0 <array.0>
(gdb) x/s 0x5555555571bf
0x5555555571bf: "bruins"
(gdb) x/s 0x5555555571f0
0x5555555571f0 <array.0>: "maduiersnfotvbylSo you think you can stop the bomb with ctrl-c, do you?"
(gdb)
To summarize the transformation process:
- The function takes each byte of the string
- It keeps only the least significant 4 bits of each byte
- It uses these 4 bits as an index into the lookup table (
array.0) - The value from the array is then stored in a buffer
Here's how the transformation process can be reversed for each character in "bruins":
1. Find the index of b in the lookup table (in our case, it is 13 since we index starting 0)
2. Calculate binary representation of this index (in our case 13 can be written as 1101 in binary)
3. Find ASCII character whose least significant 4 bits match (in our case, m has binary representation 01101101)
Repeat for all 6 characters
Hint: Using an ASCII - Binary Table can save you time.
Thus, we can have the following transformation:
b -> m
r -> f
u -> c
i -> d
n -> h
s -> g
Let us try out this answer:
...
That's number 2. Keep going!
Halfway there!
So you got that one. Try this one.
mfcdhg
Breakpoint 1, 0x0000555555555830 in phase_5 ()
(gdb) continue
Continuing.
Good work! On to the next...
Awesome!
Phase 6
Good work! On to the next...
test string
Breakpoint 1, 0x0000555555555899 in phase_6 ()
(gdb) disas phase_6
Dump of assembler code for function phase_6:
=> 0x0000555555555899 <+0>: endbr64
0x000055555555589d <+4>: push %r15
0x000055555555589f <+6>: push %r14
0x00005555555558a1 <+8>: push %r13
0x00005555555558a3 <+10>: push %r12
0x00005555555558a5 <+12>: push %rbp
0x00005555555558a6 <+13>: push %rbx
0x00005555555558a7 <+14>: sub $0x68,%rsp
0x00005555555558ab <+18>: lea 0x40(%rsp),%rax
0x00005555555558b0 <+23>: mov %rax,%r14
0x00005555555558b3 <+26>: mov %rax,0x8(%rsp)
0x00005555555558b8 <+31>: mov %rax,%rsi
0x00005555555558bb <+34>: call 0x555555555d97 <read_six_numbers>
0x00005555555558c0 <+39>: mov %r14,%r12
0x00005555555558c3 <+42>: mov $0x1,%r15d
0x00005555555558c9 <+48>: mov %r14,%r13
0x00005555555558cc <+51>: jmp 0x555555555997 <phase_6+254>
0x00005555555558d1 <+56>: call 0x555555555d4a <explode_bomb>
0x00005555555558d6 <+61>: jmp 0x5555555559a9 <phase_6+272>
0x00005555555558db <+66>: add $0x1,%rbx
0x00005555555558df <+70>: cmp $0x5,%ebx
0x00005555555558e2 <+73>: jg 0x55555555598f <phase_6+246>
0x00005555555558e8 <+79>: mov 0x0(%r13,%rbx,4),%eax
0x00005555555558ed <+84>: cmp %eax,0x0(%rbp)
0x00005555555558f0 <+87>: jne 0x5555555558db <phase_6+66>
0x00005555555558f2 <+89>: call 0x555555555d4a <explode_bomb>
0x00005555555558f7 <+94>: jmp 0x5555555558db <phase_6+66>
0x00005555555558f9 <+96>: mov 0x8(%rsp),%rdx
0x00005555555558fe <+101>: add $0x18,%rdx
0x0000555555555902 <+105>: mov $0x7,%ecx
0x0000555555555907 <+110>: mov %ecx,%eax
0x0000555555555909 <+112>: sub (%r12),%eax
0x000055555555590d <+116>: mov %eax,(%r12)
0x0000555555555911 <+120>: add $0x4,%r12
0x0000555555555915 <+124>: cmp %r12,%rdx
0x0000555555555918 <+127>: jne 0x555555555907 <phase_6+110>
0x000055555555591a <+129>: mov $0x0,%esi
0x000055555555591f <+134>: mov 0x40(%rsp,%rsi,4),%ecx
0x0000555555555923 <+138>: mov $0x1,%eax
0x0000555555555928 <+143>: lea 0x3d01(%rip),%rdx # 0x555555559630 <node1>
--Type <RET> for more, q to quit, c to continue without paging--
0x000055555555592f <+150>: cmp $0x1,%ecx
0x0000555555555932 <+153>: jle 0x55555555593f <phase_6+166>
0x0000555555555934 <+155>: mov 0x8(%rdx),%rdx
0x0000555555555938 <+159>: add $0x1,%eax
0x000055555555593b <+162>: cmp %ecx,%eax
0x000055555555593d <+164>: jne 0x555555555934 <phase_6+155>
0x000055555555593f <+166>: mov %rdx,0x10(%rsp,%rsi,8)
0x0000555555555944 <+171>: add $0x1,%rsi
0x0000555555555948 <+175>: cmp $0x6,%rsi
0x000055555555594c <+179>: jne 0x55555555591f <phase_6+134>
0x000055555555594e <+181>: mov 0x10(%rsp),%rbx
0x0000555555555953 <+186>: mov 0x18(%rsp),%rax
0x0000555555555958 <+191>: mov %rax,0x8(%rbx)
0x000055555555595c <+195>: mov 0x20(%rsp),%rdx
0x0000555555555961 <+200>: mov %rdx,0x8(%rax)
0x0000555555555965 <+204>: mov 0x28(%rsp),%rax
0x000055555555596a <+209>: mov %rax,0x8(%rdx)
0x000055555555596e <+213>: mov 0x30(%rsp),%rdx
0x0000555555555973 <+218>: mov %rdx,0x8(%rax)
0x0000555555555977 <+222>: mov 0x38(%rsp),%rax
0x000055555555597c <+227>: mov %rax,0x8(%rdx)
0x0000555555555980 <+231>: movq $0x0,0x8(%rax)
0x0000555555555988 <+239>: mov $0x5,%ebp
0x000055555555598d <+244>: jmp 0x5555555559c4 <phase_6+299>
0x000055555555598f <+246>: add $0x1,%r15
0x0000555555555993 <+250>: add $0x4,%r14
0x0000555555555997 <+254>: mov %r14,%rbp
0x000055555555599a <+257>: mov (%r14),%eax
0x000055555555599d <+260>: sub $0x1,%eax
0x00005555555559a0 <+263>: cmp $0x5,%eax
0x00005555555559a3 <+266>: ja 0x5555555558d1 <phase_6+56>
0x00005555555559a9 <+272>: cmp $0x5,%r15d
0x00005555555559ad <+276>: jg 0x5555555558f9 <phase_6+96>
0x00005555555559b3 <+282>: mov %r15,%rbx
0x00005555555559b6 <+285>: jmp 0x5555555558e8 <phase_6+79>
0x00005555555559bb <+290>: mov 0x8(%rbx),%rbx
0x00005555555559bf <+294>: sub $0x1,%ebp
0x00005555555559c2 <+297>: je 0x5555555559d5 <phase_6+316>
0x00005555555559c4 <+299>: mov 0x8(%rbx),%rax
0x00005555555559c8 <+303>: mov (%rax),%eax
0x00005555555559ca <+305>: cmp %eax,(%rbx)
--Type <RET> for more, q to quit, c to continue without paging--
0x00005555555559cc <+307>: jge 0x5555555559bb <phase_6+290>
0x00005555555559ce <+309>: call 0x555555555d4a <explode_bomb>
0x00005555555559d3 <+314>: jmp 0x5555555559bb <phase_6+290>
0x00005555555559d5 <+316>: add $0x68,%rsp
0x00005555555559d9 <+320>: pop %rbx
0x00005555555559da <+321>: pop %rbp
0x00005555555559db <+322>: pop %r12
0x00005555555559dd <+324>: pop %r13
0x00005555555559df <+326>: pop %r14
0x00005555555559e1 <+328>: pop %r15
0x00005555555559e3 <+330>: ret
End of assembler dump.
(gdb)
Again, we see the familiar read_six_digits function.
Let us analyse this function in chunks:
0x00005555555558bb <+34>: call 0x555555555d97 <read_six_numbers>
0x00005555555558c0 <+39>: mov %r14,%r12
0x00005555555558c3 <+42>: mov $0x1,%r15d
0x00005555555558c9 <+48>: mov %r14,%r13
0x00005555555558cc <+51>: jmp 0x555555555997 <phase_6+254>
- Read six numbers
- Initialise Registers:
2.1.
mov %r14,%r12:%r14should be pointing to the location of the stack where the numbers were read into. This address is copied onto%r122.2.mov $0x1,%r15d: The value1is moved into%r15register (probably acting like a counter) 2.3.mov %r14,%r13: The value is also copied to%r13 - Jump to start of loop:
0x0000555555555997 <+254>: mov %r14,%rbp
0x000055555555599a <+257>: mov (%r14),%eax
0x000055555555599d <+260>: sub $0x1,%eax
0x00005555555559a0 <+263>: cmp $0x5,%eax
0x00005555555559a3 <+266>: ja 0x5555555558d1 <phase_6+56>
- Initialise register and point to first number in sequence
- Adjust number(s):
2.1.
mov (%r14),%eax-> load the current number in the sequence 2.2.sub $0x1,%eax-> decrement number by 1 - Validation
3.1.
cmp $0x5,%eax: This compares the adjusted value in%eaxwith 5. 3.2.ja 0x5555555558d1 <phase_6+56>: jump if given value is > 5 or < 0
=> All numbers should be between 1 and 6.
0x00005555555559a9 <+272>: cmp $0x5,%r15d
0x00005555555559ad <+276>: jg 0x5555555558f9 <phase_6+96>
This checks if the value stored in %r15 is > 5, if it is then it jumps somewhere else. This validates our assumption that %r15 is acting as a counter.
0x00005555555559b3 <+282>: mov %r15,%rbx
0x00005555555559b6 <+285>: jmp 0x5555555558e8 <phase_6+79>
Let us jump to +79
0x00005555555558e8 <+79>: mov 0x0(%r13,%rbx,4),%eax
0x00005555555558ed <+84>: cmp %eax,0x0(%rbp)
0x00005555555558f0 <+87>: jne 0x5555555558db <phase_6+66>
0x00005555555558f2 <+89>: call 0x555555555d4a <explode_bomb>
0x00005555555558f7 <+94>: jmp 0x5555555558db <phase_6+66>
This section deals with checking if all the numbers in the sequence are unique or not. Thus, we need to ensure out 6 digits are unique
0x00005555555558db <+66>: add $0x1,%rbx // Increments by 1
0x00005555555558df <+70>: cmp $0x5,%ebx
0x00005555555558e2 <+73>: jg 0x55555555598f <phase_6+246> // Jump if > 5 (Loop iterations are complete)
0x00005555555558e8 <+79>: mov 0x0(%r13,%rbx,4),%eax
0x00005555555558ed <+84>: cmp %eax,0x0(%rbp)
0x00005555555558f0 <+87>: jne 0x5555555558db <phase_6+66> // Again, check if the number being seen is unique
Now we know that the numbers are unique, between 1-6 (inclusive).
After stepping through the instructions, we can also see that the numbers are being transformed: * By subtracting it from 7 (mov $0x7,%ecx followed by sub (%r12),%eax) * This effectively maps the numbers as follows: 1 to 6, 2 to 5, 3 to 4, 4 to 3, 5 to 2, and 6 to 1.
Let us try to figure out what 0x0000555555555928 <+143>: lea 0x3d01(%rip),%rdx # 0x555555559630 <node1> is:
(gdb) x/30wx 0x555555559630
0x555555559630 <node1>: 0x000000d9 0x00000001 0x55559640 0x00005555
0x555555559640 <node2>: 0x000003ab 0x00000002 0x55559650 0x00005555
0x555555559650 <node3>: 0x0000014f 0x00000003 0x55559660 0x00005555
0x555555559660 <node4>: 0x000000a1 0x00000004 0x55559670 0x00005555
0x555555559670 <node5>: 0x000001b3 0x00000005 0x55559120 0x00005555
0x555555559680 <host_table>: 0x555573f5 0x00005555 0x5555740f 0x00005555
0x555555559690 <host_table+16>: 0x55557429 0x00005555 0x00000000 0x00000000
0x5555555596a0 <host_table+32>: 0x00000000 0x00000000
(gdb) x/30wx 0x555555559120
0x555555559120 <node6>: 0x000002da 0x00000006 0x00000000 0x00000000
0x555555559130: 0x00000000 0x00000000 0x00000000 0x00000000
0x555555559140 <userid>: 0x61767861 0x38383535 0x00000000 0x00000000
0x555555559150 <userid+16>: 0x00000000 0x00000000 0x00000000 0x00000000
0x555555559160 <userid+32>: 0x00000000 0x00000000 0x00000000 0x00000000
0x555555559170 <userid+48>: 0x00000000 0x00000000 0x00000000 0x00000000
0x555555559180 <userid+64>: 0x00000000 0x00000000 0x00000000 0x00000000
0x555555559190 <userid+80>: 0x00000000 0x00000000
(gdb)
It appears that this is a linked list. With roughly the following structure:
struct node {
int value;
int index;
struct node *next;
};
Let us convert the values into decimal:
0x000000d9 -> 217
0x000003ab -> 939
0x0000014f -> 335
0x000000a1 -> 161
0x000001b3 -> 435
0x000002da -> 730
Missing Notes
To re-arrange this linked list in descending order, we would arrange it as follows:
Node 2 -> Node 6 -> Node 5 -> Node 3 -> Node 1 -> Node 4
Since we also need to apply the transformation: 7 - x:
(7-2) -> (7-6) -> ... -> (7-4)
Final answer: 5 1 2 4 6 3
Let us try the answer:
...
That's number 2. Keep going!
Halfway there!
So you got that one. Try this one.
Good work! On to the next...
5 1 2 4 6 3
Breakpoint 1, 0x0000555555555899 in phase_6 ()
(gdb) continue
Continuing.
Congratulations! You've defused the bomb!
Your instructor has been notified and will verify your solution.
[Inferior 1 (process 1754) exited normally]
But, what about the secret phase?
